For many years, midstream operators have been conducting cyber vulnerability assessments to identify risks in the digital field architecture. Likewise, these same operators are required to conduct consequence analyses and a host of other pipeline integrity assessments. This article explores the value of examining those findings through a combined lens and the ability to comprehensively address and mitigate risks.
Midstream operators have conducted cyber vulnerability assessments on operational technology (OT) assets for the past two decades. These assessments, separate from the business and enterprise networks, are considered mission critical. Essential to ensuring continuity of operations, these assets are also high-value targets to adversaries. Whether meeting safety goals and corporate values or meeting federal guidance or directives, the importance of identifying and mitigating risks is evident.
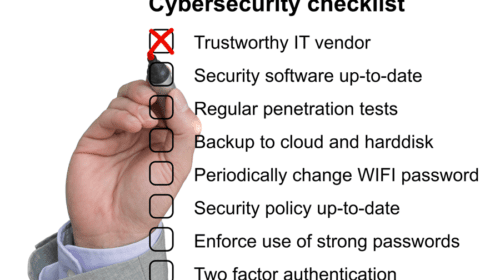
Cyber vulnerability assessments typically include penetration testing and scanning tools that, in conjunction with the technical skills of an assessment team, produce a list of vulnerabilities. These vulnerabilities include the operating system, application and network vulnerabilities. Assessments also identify risks such as open ports, default passwords, access control weaknesses, and gaps in patching. Assessment findings indicate the current security posture – or a snapshot – of a system, network or complete digital architecture.
Assessments utilizing the risk equation, R(f) = T x V x C, where Risk is a function of Threat, Vulnerability and Consequence, result in actionable mitigation findings. Reducing cyber vulnerabilities in mission critical assets means reducing overall risk to operations. Some significant challenges can exist, however, in applying those mitigations. Many operators do not maintain a fully prioritized list of sites and assets in enough depth to assign values. This requires a clear asset inventory, including technology and data, as well as consideration of highest value operations, federal determination of site criticality, and supply chain dependencies.
Because cyber vulnerability assessments in the OT environment are often commissioned or conducted by technical staff, a broader view of the overall risk portfolio of the organization may not exist. While mitigating all risks is ideal, realistically, organizations must prioritize mitigations around budget and time constraints. Choosing mitigations that provide the best return on investment by adding to stability, safety and operational continuity is essential.
Identifying and mitigating risks in the highest valued operational areas requires a view of individual pipelines, segments, sites, throughput and technology assets within the operation. Pipeline integrity assessments may be an excellent place to obtain that view.
The paradigm shift in perceiving and addressing cybersecurity in relation to pipeline integrity was catalyzed by the infamous cyberattack on the Colonial Pipeline in 2021. This unprecedented event exposed critical vulnerabilities in asset management within the energy transport industry, compelling major operators and government entities to take proactive measures in updating and establishing standards and regulations.
Pipeline transportation remains the most secure and dependable method for transporting energy resources. However, with the aging of pipeline assets and the emergence of novel threats jeopardizing the safety and reliability of these systems, the significance of managing pipeline integrity with a risk-based approach has become more imperative and intricate than ever before.
Identifying and assessing potential threats to pipelines and associated facilities pose a formidable challenge for operators. A paramount concern lies in acquiring and utilizing reliable data for conducting thorough threat assessments. The effectiveness of an integrity management program hinges on the quality and availability of such data. Presently, operators have access to a range of tools to enhance their capabilities in preventing, detecting and responding to cyber incidents. To effectively manage the integrity of assets, it is crucial to comprehend the risks associated with potential events, assess their consequences, and establish robust risk management strategies.
Upon establishing a risk model for their pipeline assets, operators must recognize cybersecurity threats, irrespective of the complexity of the risk model or the size of the asset. Two primary objectives while evaluating this threat involve gauging the criticality of the asset in terms of availability and assessing the current level of awareness and knowledge regarding potential threats to the asset.
Throughout this process, operators may lack awareness of vulnerabilities and cyber threats. In such cases, it is prudent to conduct comprehensive gap analyses to compare the existing situation with the desired target state and devise appropriate action plans to bridge any identified gaps.
Combining pipeline security and integrity assessments and analyses produces findings that establish a complete view of risk. This approach offers a manageable view of operational complexities by aligning critical pipeline assets, integrity data, and security zones and conduits. This can be a powerful, comprehensive view that:
- provides the basis for risk-based business and operational decisions
- establishes ROI for security and capital investments
- assists in meeting compliance goals
Security and integrity assessment teams, working together, can streamline data collection, assessments and evaluation of findings. Deliverables and output from a combined approach can assist the customer to identify and prioritize:
- operational dependencies
- mission-critical assets
- potential consequences (cyber, physical, operational)
- critical failure points
The growing regulatory landscape, including industry standards and federal guidelines, expects asset owners to have a clear and accurate view of their operations and understand potential consequences. This combined approach enables pipeline operators to optimize the use of resources, both in terms of time and budget. Shared data, tools and expertise can be leveraged across the integrated assessment process, leading to greater efficiency and cost-effectiveness, while allowing an asset owner to map potential downtime or damage-related risks to operational consequences.
In addition, it assists in identifying a customer’s placement in the national critical infrastructure and supply chain, including product delivery and supply receipt impacts, as well as broader market impacts. Demonstrating a comprehensive approach to pipeline security and integrity reassures stakeholders, including investors, regulators and the public, that the operator is committed to ensuring the safe and reliable transportation of energy resources.
Overall, the convergence of pipeline security and integrity assessments and analyses empowers operators to make informed decisions, improve overall operational resilience, and maintain the integrity of their pipeline assets in an increasingly complex and dynamic threat landscape.
Annie McIntyre is an expert in operational security for critical infrastructure and the director of operational security for EverLine. Everline’s technical stack offers fully integrated compliance, SCADA/IT, control room and security services. Visit EverLine at www.everlineus.com.
Romina Peverelli is Everline’s Director of Integrity Management.
Oil and gas operations are commonly found in remote locations far from company headquarters. Now, it's possible to monitor pump operations, collate and analyze seismic data, and track employees around the world from almost anywhere. Whether employees are in the office or in the field, the internet and related applications enable a greater multidirectional flow of information – and control – than ever before.